
Crypto
ezCrypto
- 差评
- 先把 map 爆破出来
|
|
-
随便逆逻辑就行了
-
随便逆出
- flaglist1 = ‘0)&3F~’
- flaglist2 = ‘1Dn1F 23m0s 4nl5OtP 7Rc’
-
flag 即为:sixstars{XXX_F1nD_s0m3_XXX_ln_cR7PtO}"
-
暴力破解,寻找张得好看的:
- sixstars{TrY_F1nD_s0m3_F4n_ln_cR7PtO}
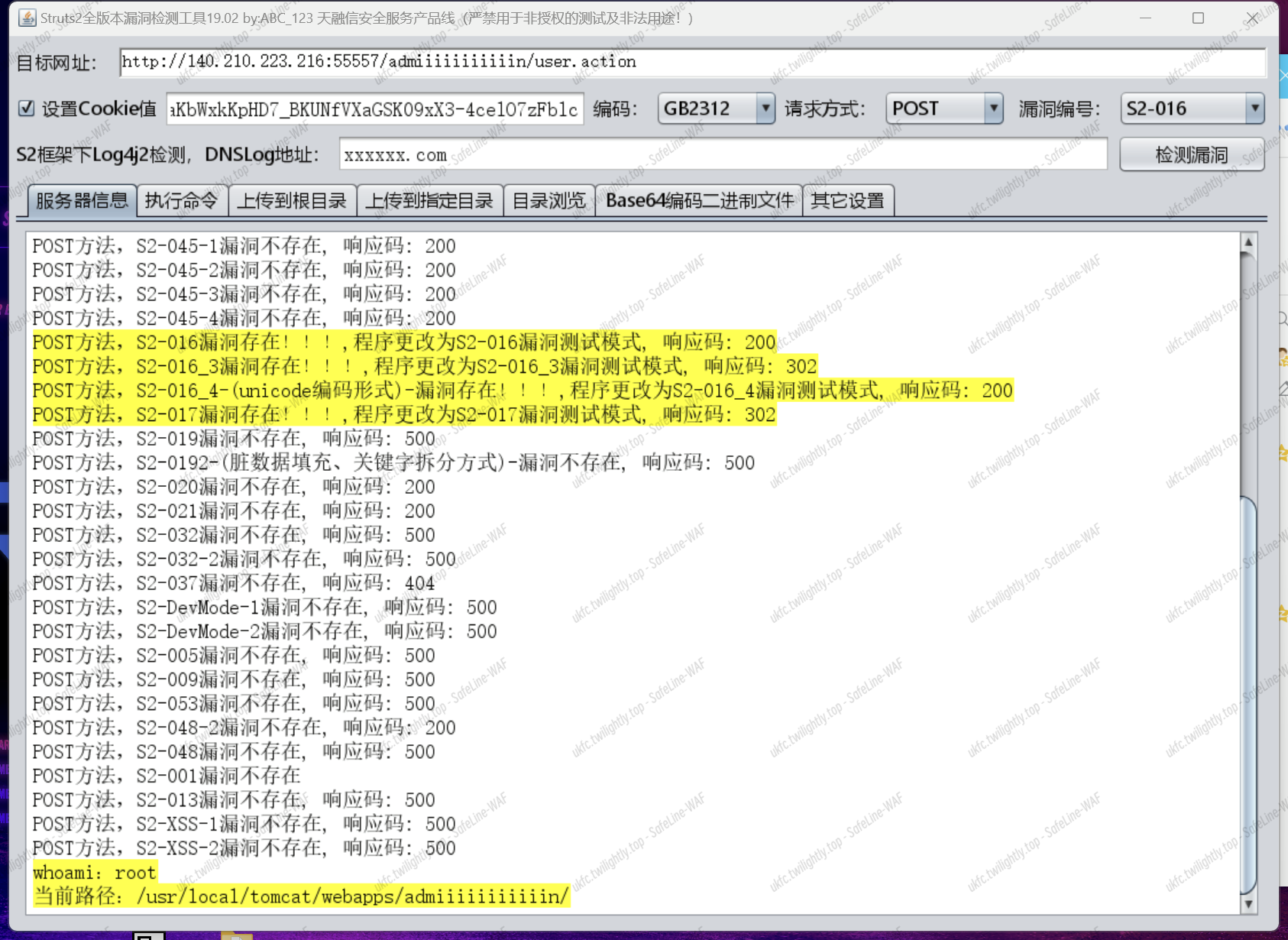
Web
jwt2struts
- 一把梭 + 伪造 jwt
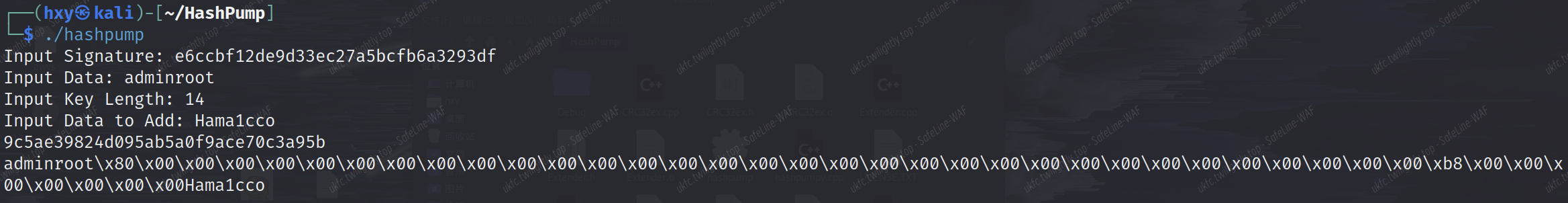
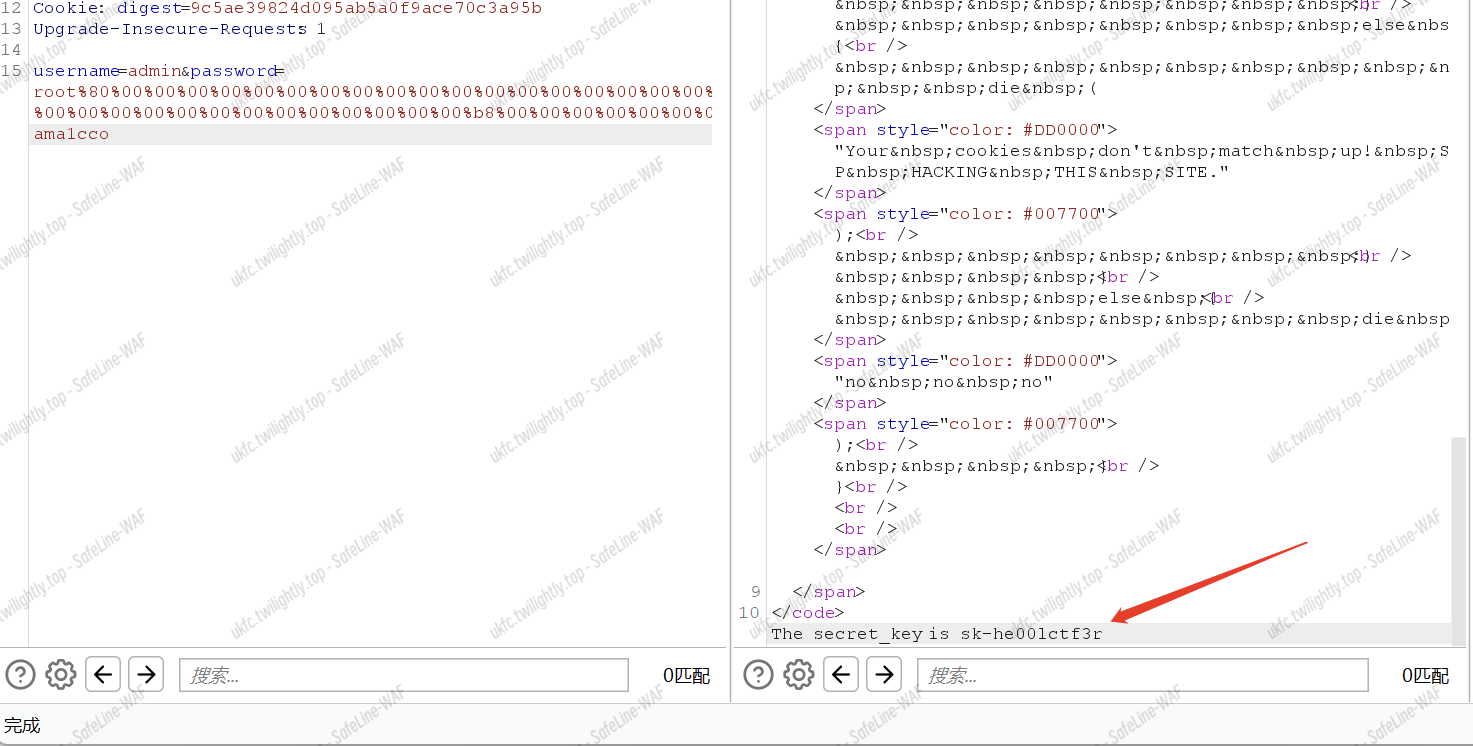
- struct2 一把梭
Misc
MWM
- AI 模型
- 提取训练数据
|
|
- 计算 flag 开头的值
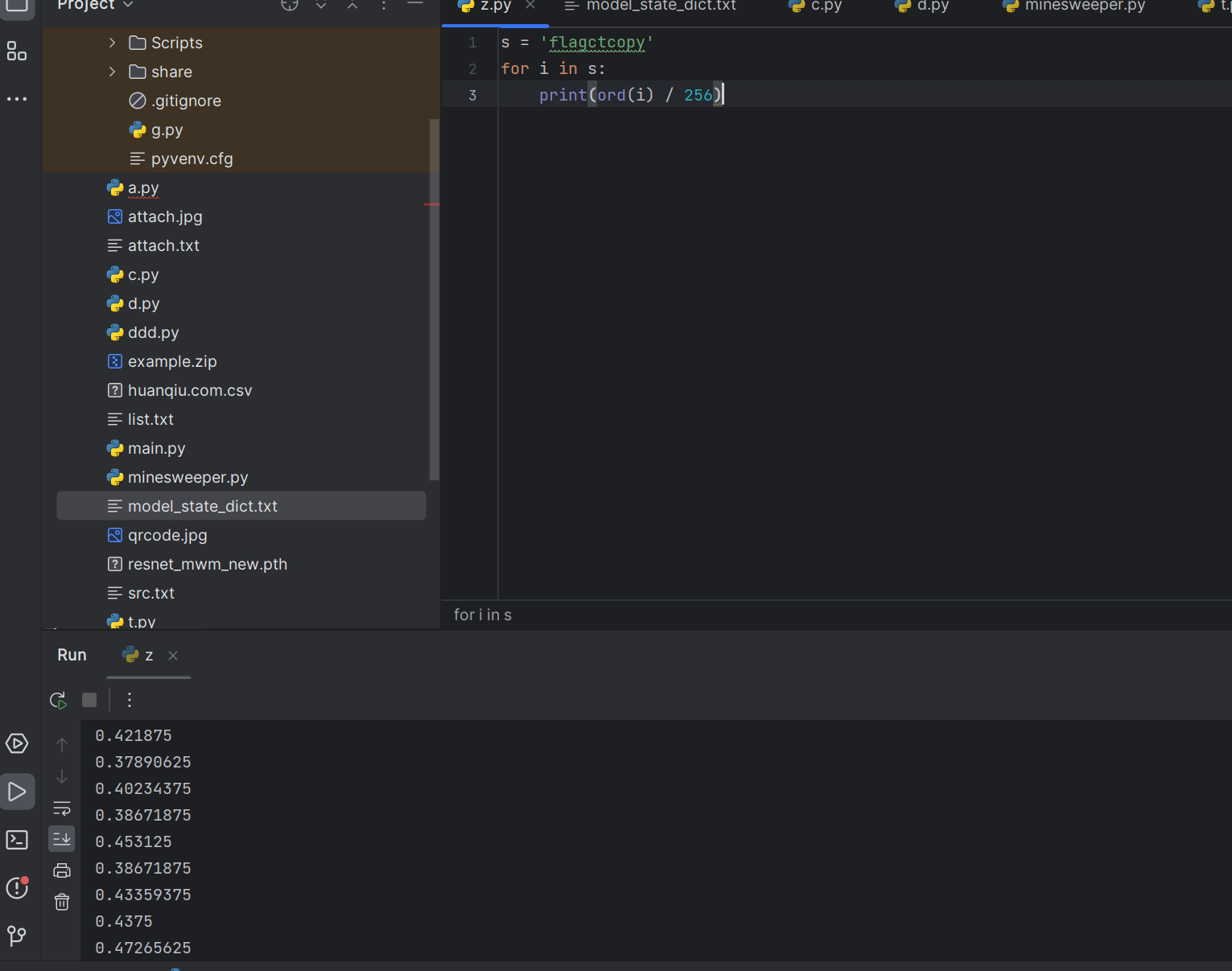
- 定位数据
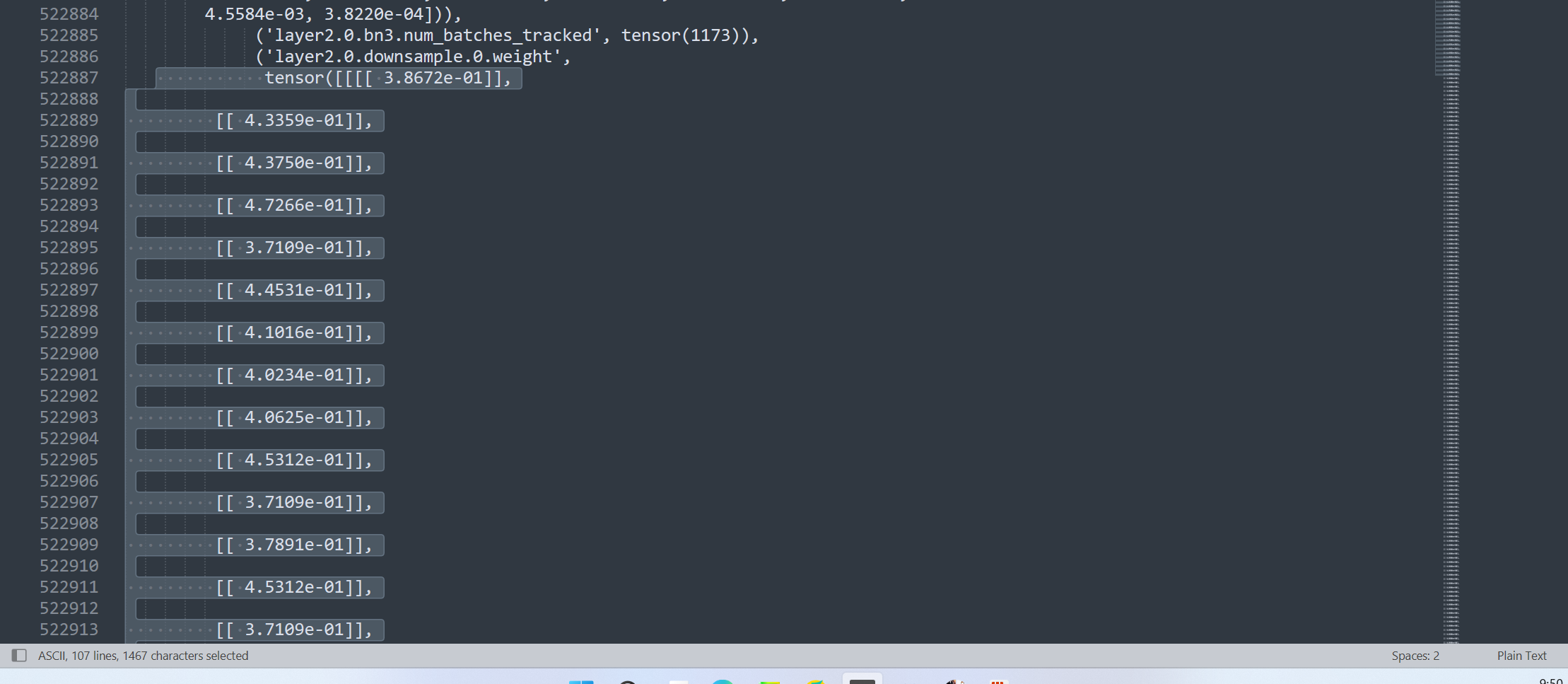
- 得到 flag
|
|
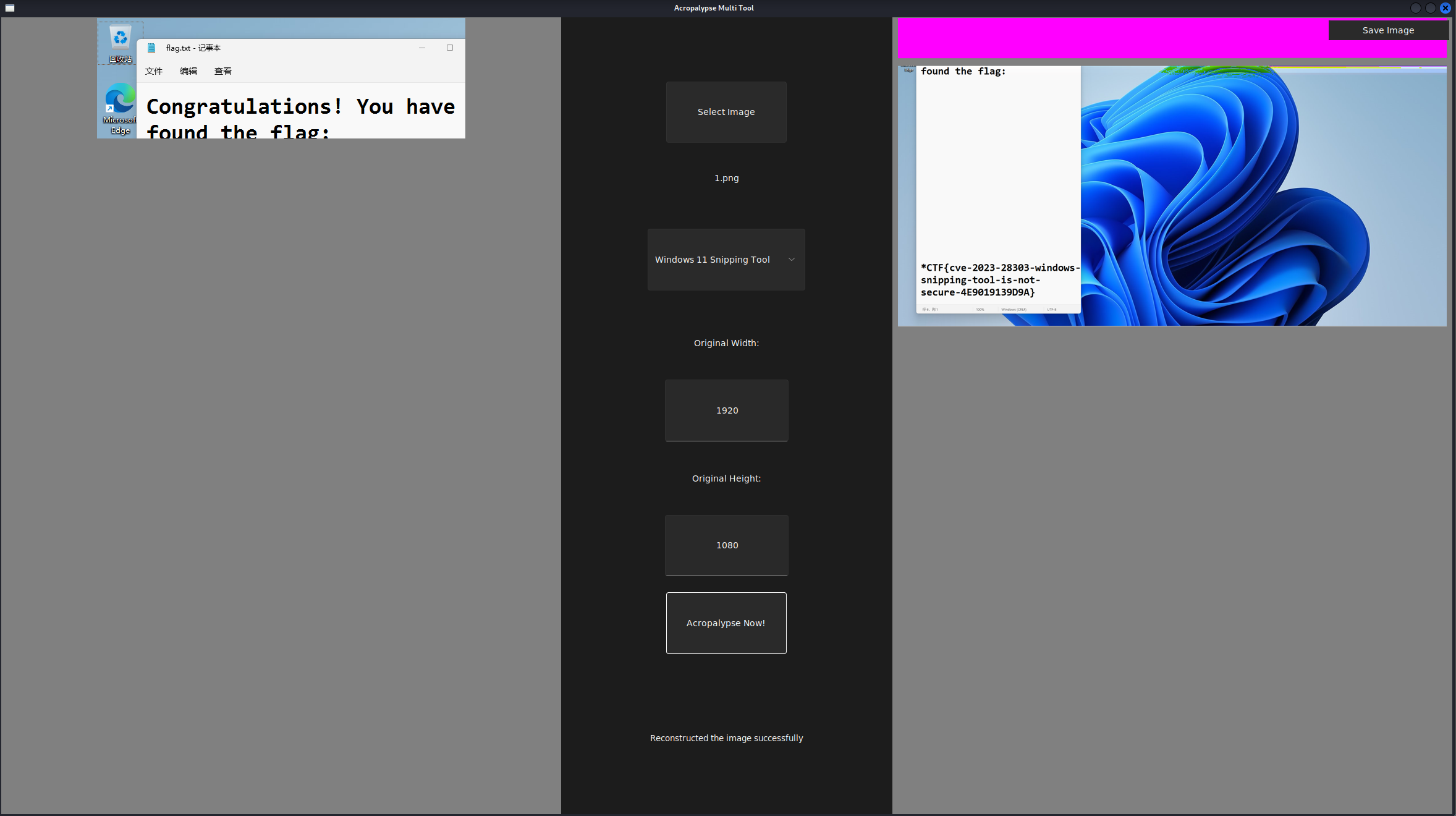
snippingTools
- CVE-2023-28303:https://github.com/frankthetank-music/Acropalypse-Multi-Tool
old language
- 龙语:
https://zh.wikipedia.org/zh-hans/%E5%A4%9A%E7%93%A6%E7%A5%96%E7%88%BE%E8%AA%9E
dead game
- 通关即可
Reverse
ez_code
- powshell 脚本,第一眼我还以为 dos 呢
- ise 把明文代码搞出来,要不看不懂
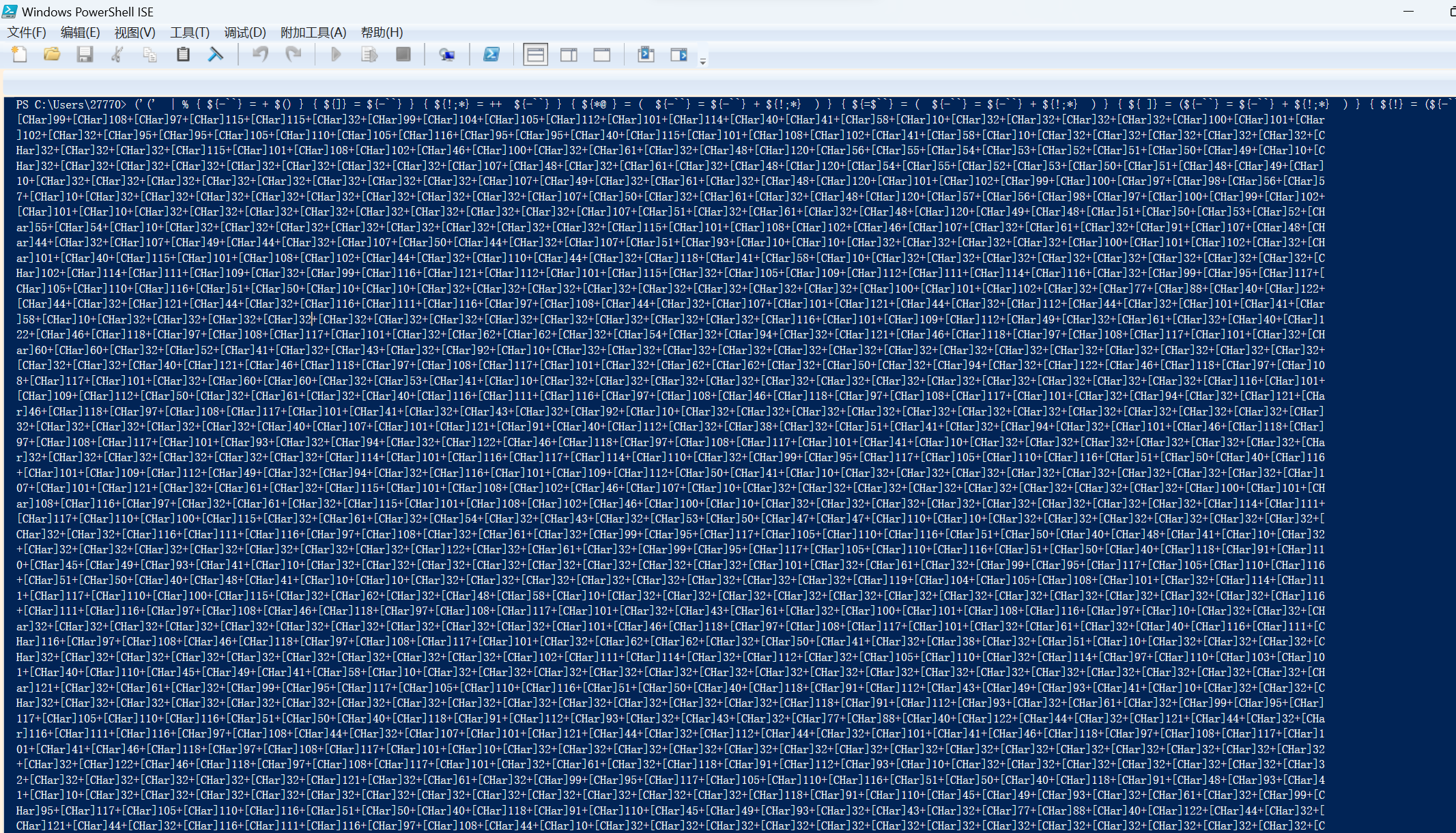
|
|
- xxtea
|
|
flagfile
010 打开,观察到 flag 格式以及匹配的大概规则
https://blog.csdn.net/qq_35677314/article/details/120687202?spm=1001.2014.3001.5501
用每一模块 leshort 两个字节异或,可以得到一串数字和一串字符串,按照数字重新排列字符串
|
|
GoGpt
go 语言,用工具恢复符号表
逻辑为:flag 与 TcR@3t_3hp_5_G1HTcR@3t_3hp_5_G1H 异或,结果 base64 之后是 fiAGBkgXN3McFy9hAHRfCwYaIjQCRDFsXC8ZYBFmEDU=
|
|
