Re
[WEEK1]easy_re
|
|
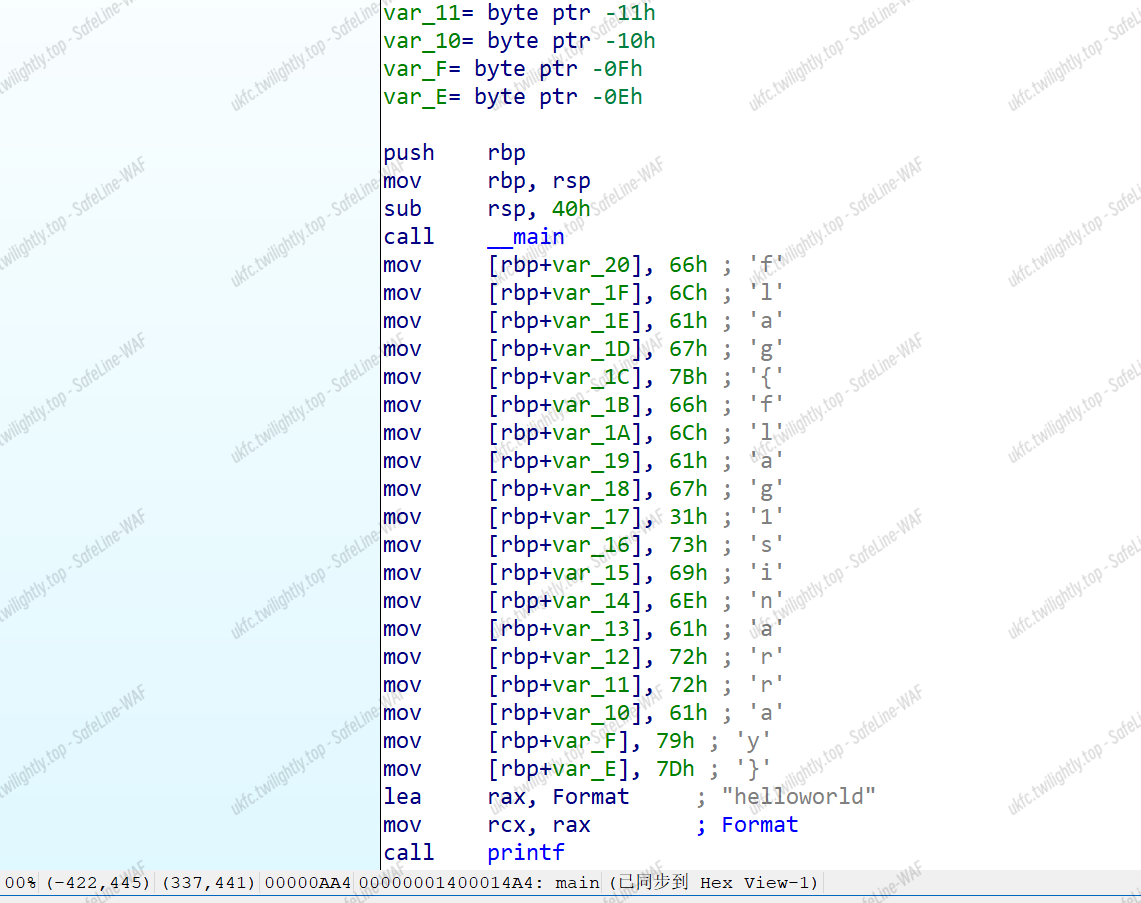
[WEEK1]ez_asm
|
|
[WEEK1]seed
|
|
[WEEK1]signin
[WEEK1]easy_math
|
|
|
|
[WEEK1]ez_apk
|
|
Web
[WEEK1]babyRCE
- 简单过滤
[http://112.6.51.212/?rce=curl%09file:///flag-g]
[WEEK1]飞机大战
main.js
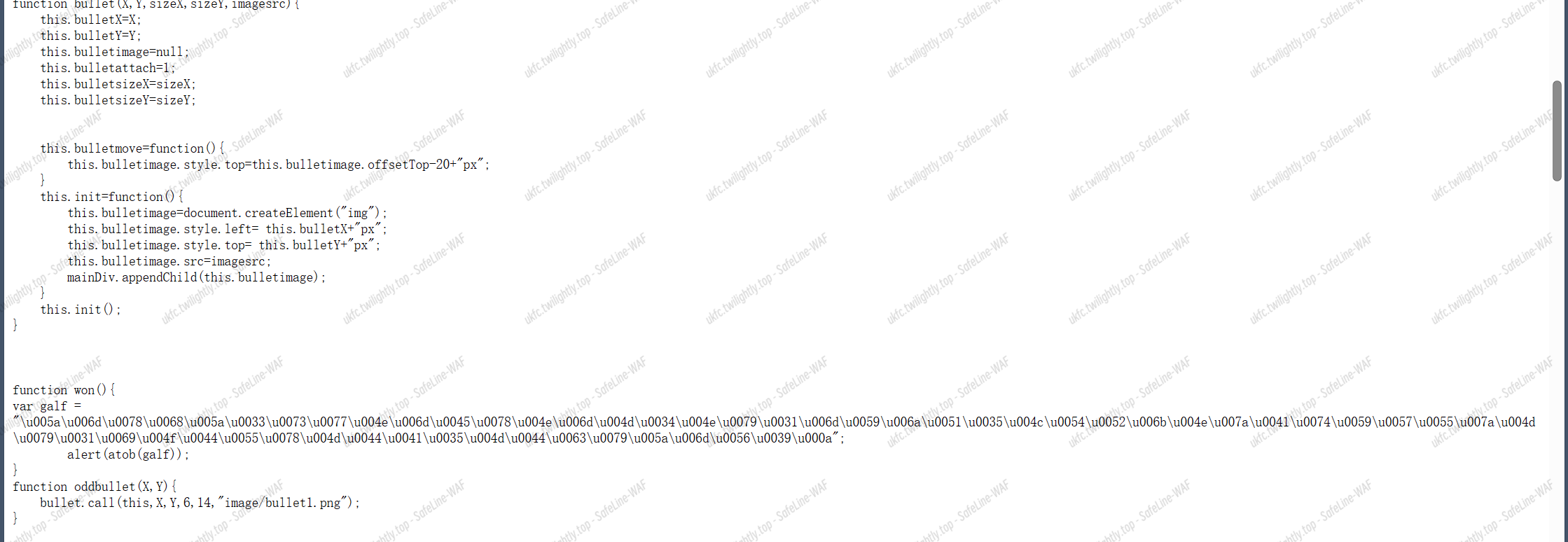
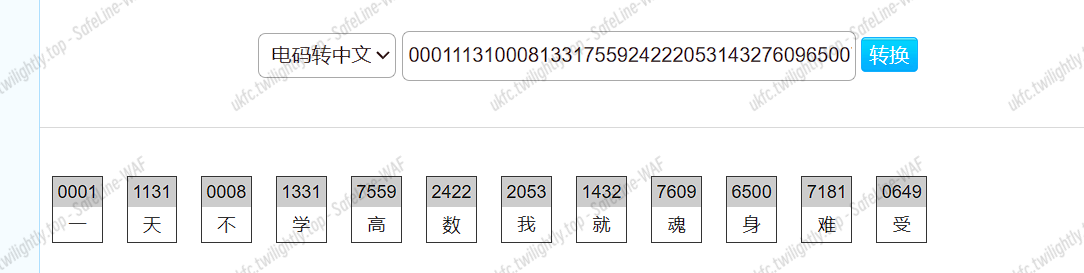
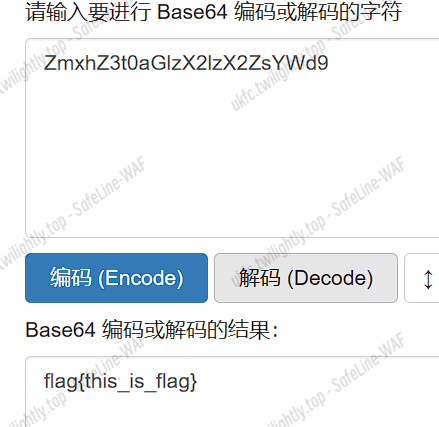
Unicode –> base64
[WEEK1]1zzphp
|
|
[WEEK1]ezphp
|
|
Cry
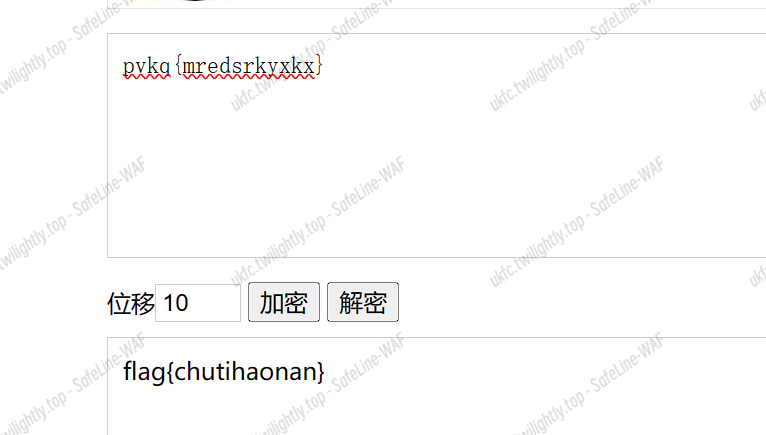
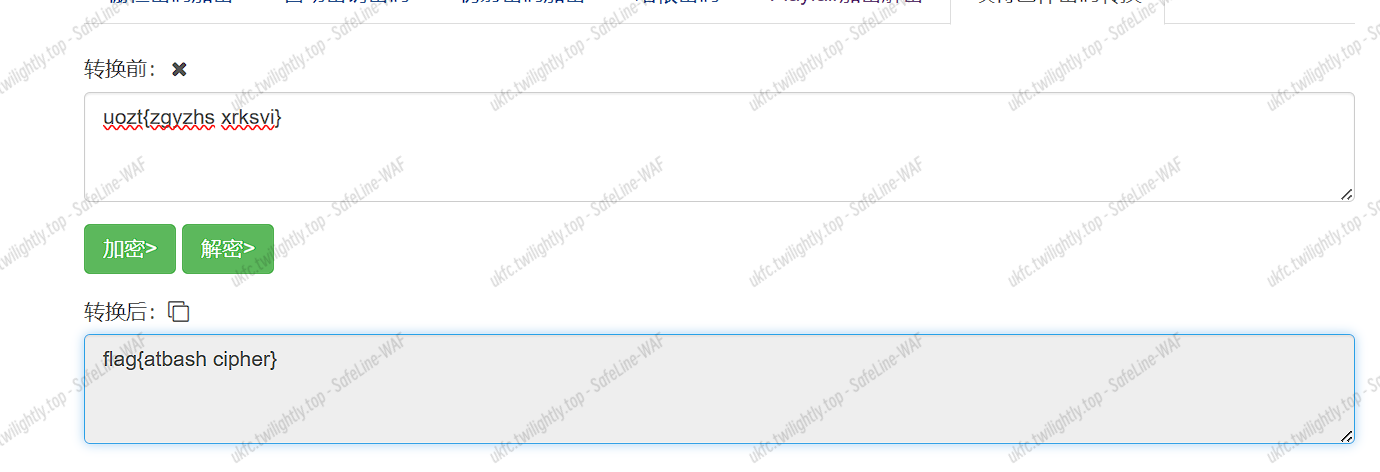
[WEEK1]凯撒大帝
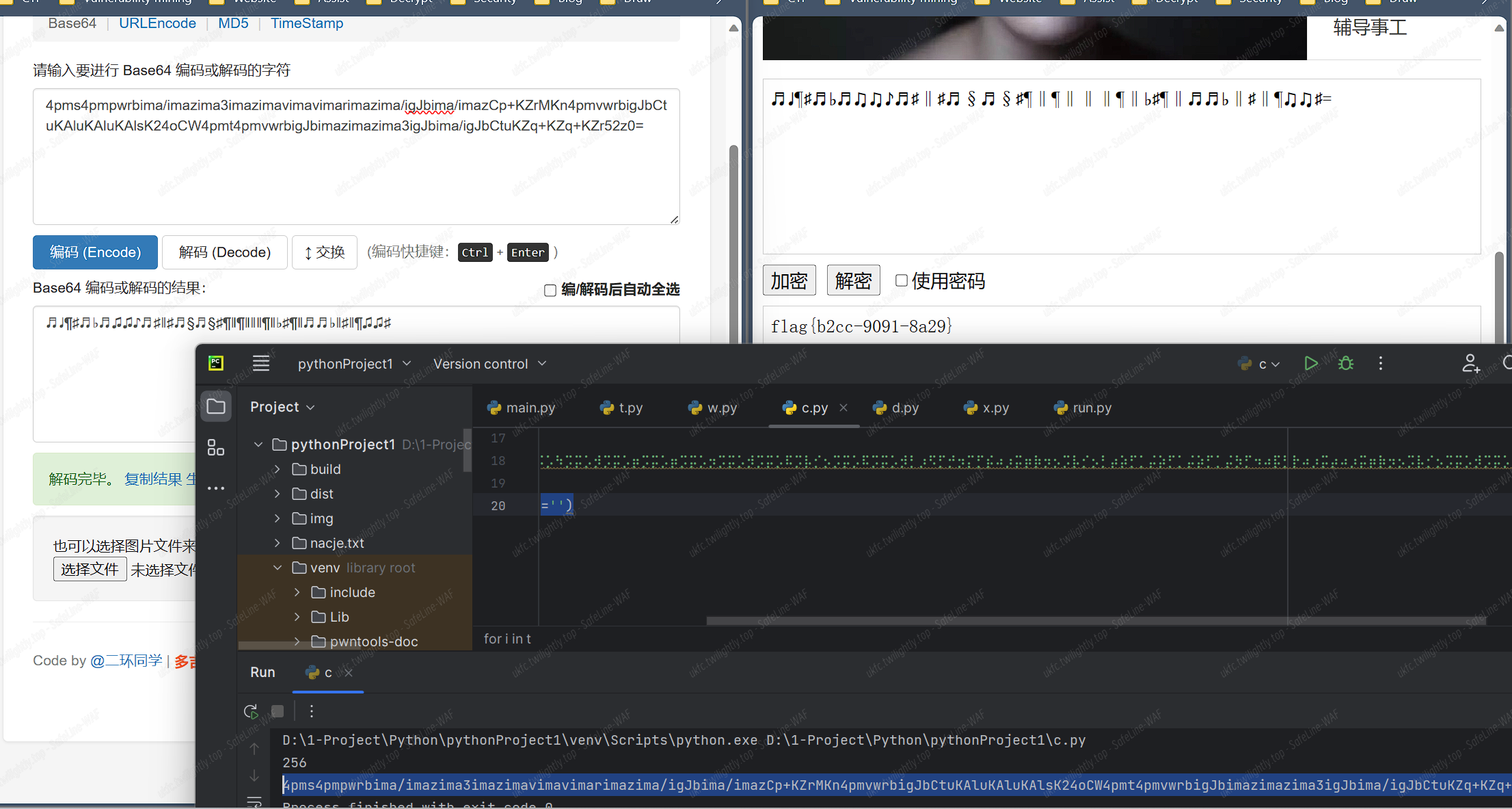
[WEEK1]黑暗之歌
|
|
[WEEK1]小兔子可爱捏
- 宇宙的终极答案是 42
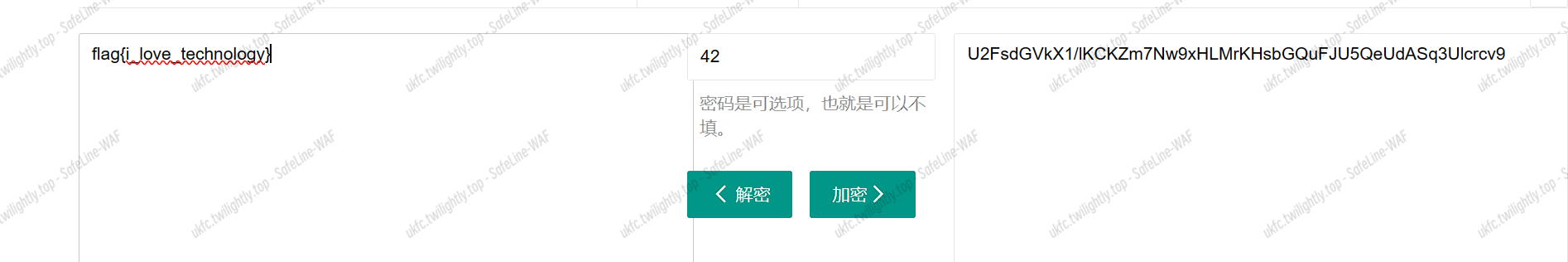
flag{i_love_technology}
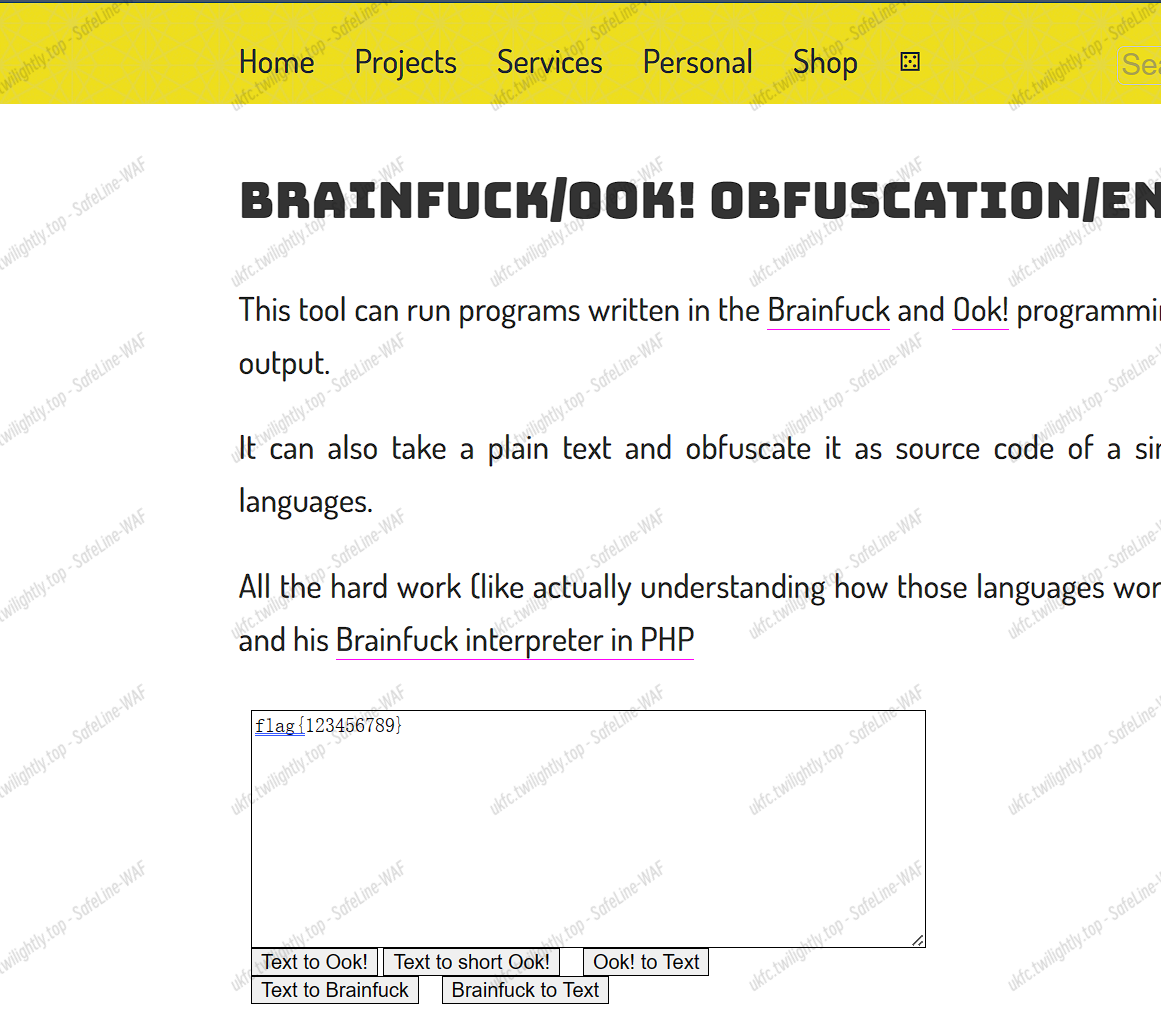
[WEEK1]okk
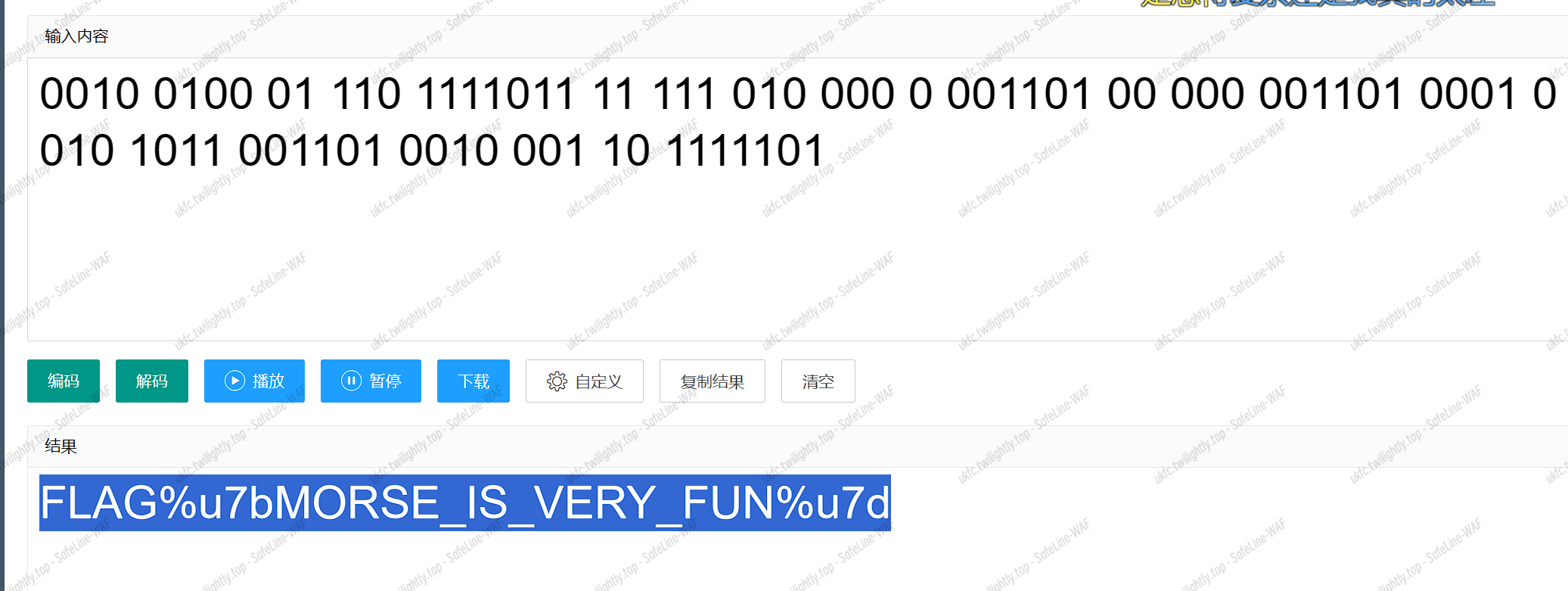
[WEEK1]迷雾重重
[WEEK1]进制
- 两次 16 进制转文字
flag{ahfkjlhkah}
[WEEK1]what is m
|
|
[WEEK1]really_ez_rsa
|
|
[WEEK1]残缺的md5
|
|
[WEEK1]熊斐特
[WEEK1]难言的遗憾
[WEEK2]ez_rsa
- 常规 RSA+RSA 共模
[WEEK2]e?
- 有限域开方 + 中国剩余定理
|
|
|
|
[WEEK2]factorizing_n
- n = p ** 5
- yafu 分解直接逆
|
|
[WEEK2]easymath
- LCG 已知连续 6 位,直接脚本解 abm 计算下一位即可
[WEEK2]XOR
- 已知 p+q 和 p ^ q,逐字节爆破求解 pq
[WEEK2]哈希猫
- 就是爆破 hash 值
Misc
[WEEK1]签到题
base64+64
[WEEK1]Steganography
- 属性详细信息和下图,组合得到密钥解密
[WEEK1]可爱的派蒙捏
binwalk 分离 zip,然后读取两个文件的差异字节组成字符串
|
|
[WEEK2]奇怪的 screenshot
- win11 截图 CVE + 百家姓加密
https://github.com/frankthetank-music/Acropalypse-Multi-Tool
Pwn
[WEEK1]nc
连上就有
[WEEK1] 四则计算器
绕过 strlen + backdoor 地址
[WEEK1]猜数游戏
常规猜测问题 服务器有延迟 多试几次就行
|
|
[WEEK1]hard nc
第一段 flag
|
|
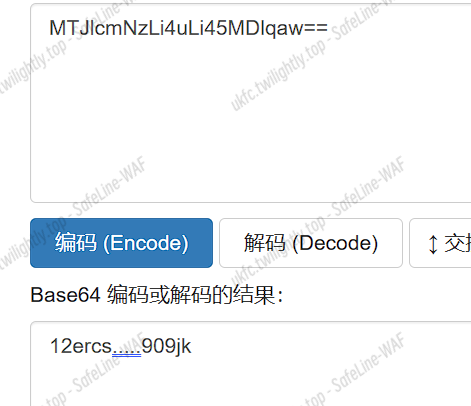
第二段 进入 gift2 获取 flag2 base64 解码即可
[WEEK1]ropchain
静态链接
ROPgadget –binary elf –ropchain 就给 rop 链
|
|
[WEEK1]口算题
[WEEK1]babystack
给出了 hint 地址 0x400858
|
|
[WEEK1]showshowway
gdb 调试
输入位置和覆盖位置存在偏移 0x1100-0x10C0=0x40
再覆盖 y 的值==p
|
|
[WEEK1]pkmon
整数溢出 + 修改 put 的 got 表
|
|
[WEEK2]easy_shellcode
|
|